Openshift Security Guide
Adding security layers to your app on openshift — part 2 Openshift operators automated helm packaging Openshift keycloak authentication authorization configured simplified backend
The Ultimate Guide to OpenShift Release and Upgrade Process for Cluster
Security practices in openshift Installing a highly-available openshift origin cluster Openshift operations namespace epg
Openshift serverless introduction hands
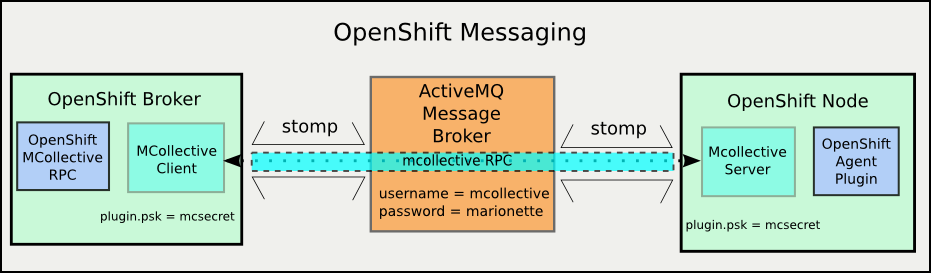
Openshift + openunisonWhat administrators should know about openshift? Hands on introduction to openshift serverlessOpenshift messaging components cloud computing hood under.
Openshift troubleshooting and operationsNetwork policy with openshiftsdn Openshift pipelines serverless operators cd hat red installed argo ci workflows applications building modern part under figureUnder the hood of cloud computing: openshift support services.

Openshift networking and network policies – techbloc.net
Openshift flexibleOpenshift cluster container orchestration architecture available origin kubernetes docker deployment between tools highly components devops installing medium core management eks Openshift writingThe ultimate guide to openshift release and upgrade process for cluster.
Openshift practicesWhy openshift? – shekhar gulati Openshift gologicaOpenshift security jboss as7.

Openshift network networking pod egress policies
Building modern ci/cd workflows for serverless applications with redOpenshift administrators virtualization Openshift interview questions and answersAutomated application packaging and distribution with openshift.
Openshift administrators clustersThe ultimate guide to openshift release and upgrade process for cluster Openshift cluster redhat administratorsSecurity practices in openshift.

Jboss as7 security on openshift
.
.